Chinese espionage growing in US healthcare: Experts
19-September-2019
After a Chinese couple was charged by the US government with stealing intellectual property related to key health data this week, cyber security researchers on Thursday raised serious questions on growing Chinese espionage in American healthcare.
The US government has charged Yu Zhou, 49, and Li Chen, 46 with theft of scientific trade secrets from Ohio's Nationwide Children's Hospital.
Zhou and Chen established their own health startup in China in 2015 while still employed with the Nationwide Children's Hospital in Ohio.
They marketed products and services related to "exosome isolation" through their Chinese startup.
Zhou and Chen allegedly used the hospital's research institute resources and equipment to conduct the exosome research necessary for their unauthorized, outside work, reports www.biospace.com.
"The indictment of the couple for allegedly stealing medical trade secrets and transferring them to China is just the latest example of a threat to the industry emanating from China," John Hultquist, Director of Intelligence Analysis at global cyber security firm FireEye, told IANS.
"In another recent publicly reported case, researchers at one institute were dismissed following similar concerns. Notably, one of the Chinese cyber espionage actors tracked by FireEye, APT41, has also demonstrated a specific interest in this field," Hultquist added.
Last month, FireEye found that there was a concerted focus on acquiring healthcare research by multiple Chinese Advanced Persistent Threat (APT) groups.
Open source reports indicate that cancer mortality rates have increased dramatically in recent decades, making cancer China's leading cause of death.
"As the People's Republic of China (PRC) continues to pursue universal healthcare by 2020, controlling costs and domestic industry will surely affect the PRC's strategy to maintain political stability," said FireEye.
"Targeting medical research and data from studies may enable Chinese corporations to bring new drugs to market faster than Western competitors," the cyber security firm said.
FireEye also found that China-based hackers broke into a leading Indian healthcare website, stealing 68 lakh records containing key patient and doctor information and credentials.
Without naming the portal, FireEye said cyber criminals were directly selling data stolen from healthcare organisations and web portals globally, including in India, in the underground markets for for under $2,000.
In early April this year, suspected Chinese cyber espionage actors targeted a US-based health centre -- with a strong focus on cancer research - with "EVILNUGGET" malware.
APT22 - a Chinese group that has focused on biomedical, pharmaceutical, and healthcare organizations in the past, and continues to be active - also targeted this same organization in prior years.
In the same month, several researchers at the MD Anderson Cancer Research were dismissed following concerns over theft of medical research on behalf of the Chinese government.
"At a time when much of China's cyber espionage for commercial purposes in the West has been restrained, these continued incidents stand out as a priority for the state," Hultquist told IANS.
"Given the use of cyber espionage and human intelligence assets to collect against these targets, it appears China is willing to flout the rules to seize the high ground in the biomedical field," he added.IANS
PM Modi Applauds Maiden Voyage of Stitched-Ship INSV Kaundinya From Porbandar to Oman
Unnao Rape Case: 'Don't Let Hate Bury The Truth', Pleads Sengar's Daughter In Viral Open Letter
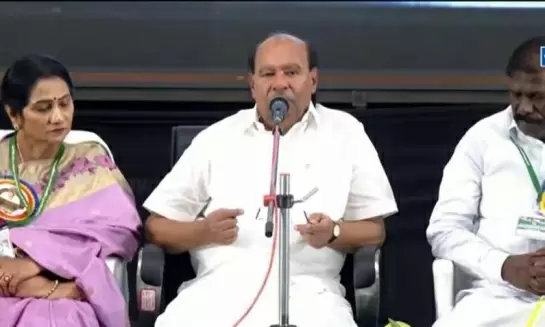
PMK Leader Dr Ramadoss Says Alliance Decision Soon, Launches Sharp Attack On Son Anbumani
Four Juveniles Held for Brutal Sickle Attack on Man Near Tiruttani Railway Station
Bangladesh Army Watches As Yunus Administration Grapples With Violence, Chaos